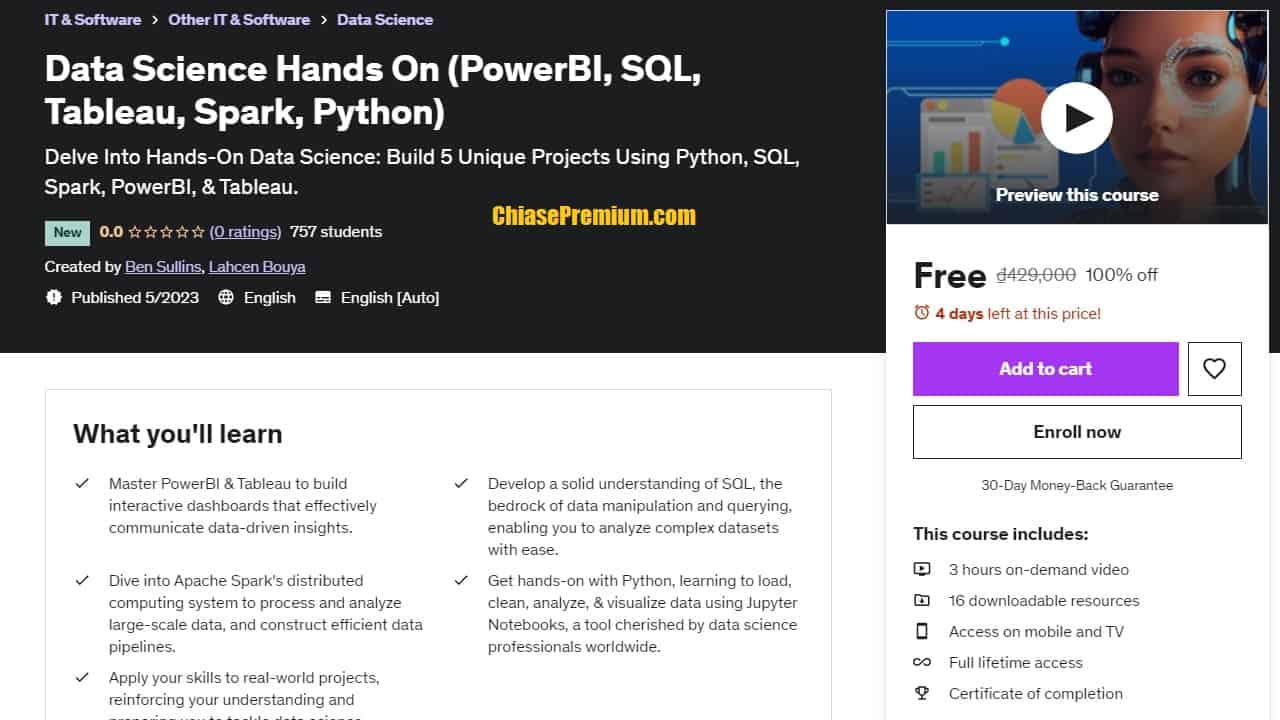
Data science ,Analytics & AI Real world Project using Python
Master AI , Data Analytics , Machine Learning & Data Sceince by solving Real-Life Analytics Problems using Python. (source: udemy.com)
What you’ll learn
- Go from zero to hero in Entire Pipeline of AI/Data Science/Machine learning from Data Collection to building a Machine Learning Model
- Various Feature Engineering Techniques & how to apply it in Real-World
- How to Approach a problem in Real-world..
- Solve any problem in your business, job or in real-time with powerful Data Sceince & Machine Learning algorithms
- Case studies
Description
This is the first course that gives hands-on Data Science, Analytics & AI Real world Projects using Python..
This is a practical course, the course I wish I had when I first started learning Data Science.
It focuses on understanding all the basic theory and programming skills required as a Data Scientist, but the best part is that it has Practical Case Studies covering so many common business problems faced by Data Scientists in the real world.
This course will cover the following topics:-
- All basic stuffs of Python
- Loops and conditionals
- Functions
- Working with Text data using Regular expressions
- Numpy ,seaborn, matplotlib ,plotly and pandas library
- Some Other fancy libraries like- fuzzywuzzy
Along with python programming, this course will cover other data analytics concepts such as
- Data Visualization
- Data cleaning
- Query Analysis
- Data Exploration
- Statistics and Probability concepts
- Feature Engineering
- Featurization
- Natural Language Processing
- Machine Learning
- Model Hypertuning
Data Scientist has become the top job in the US for the last 4 years running!” according to Harvard Business Review & Glassdoor.
This course seeks to fill all those gaps in knowledge that scare off beginners and simultaneously apply your knowledge of Data Science , Machine Learning , Data analysis ,, Natural Language Processing to real-world business problems.
Who this course is for:
- Beginners of Data Science
- Data Analysts / Business Analysts who wish to do more with their data
- College graduates who lack real world experience
- Software Developers or Engineers who’d like to start learning Data Science
- Anyone looking to become more employable as a Data Scientist
- Anyone with an interest in using Data to Solve Real World Problems
Who this course is for:
- Data Scientists who want to apply their knowledge on Real World Case Studies
(source: Udemy.com)
Link đăng ký miễn phí (ngày 30/3/2022, 1000 slots đăng ký đầu tiên):
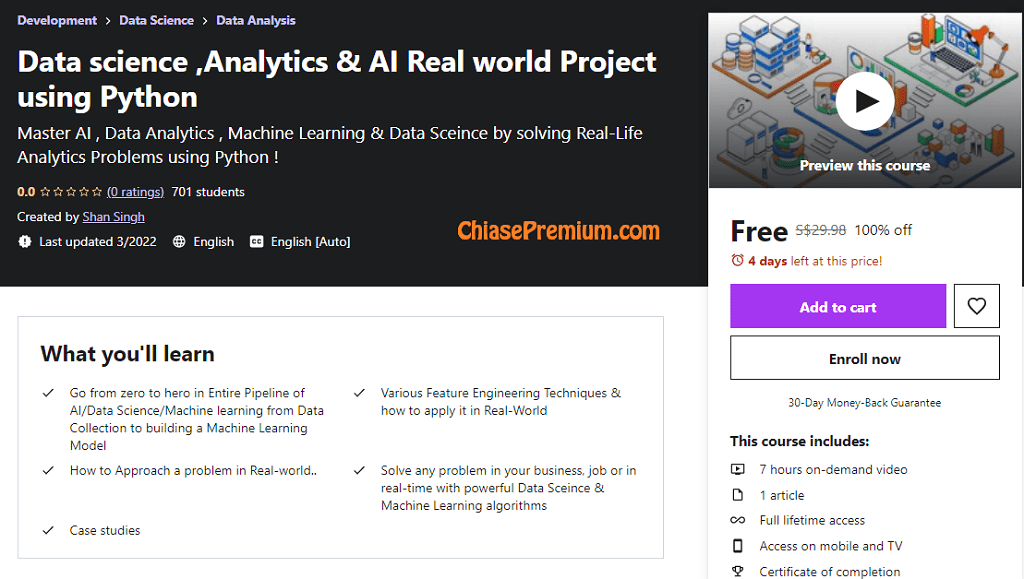
Ethical Hacking Foundation – Part 1
“An Insight into the OSI Model and Protocol Suite!
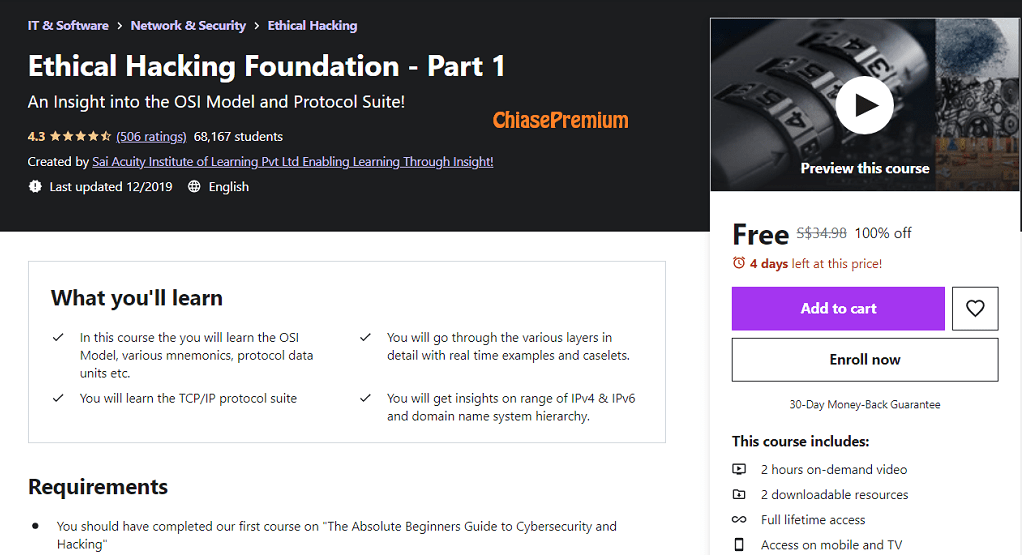
What you’ll learn
- In this course the you will learn the OSI Model, various mnemonics, protocol data units etc.
- You will go through the various layers in detail with real time examples and caselets.
- You will learn the TCP/IP protocol suite
- You will get insights on range of IPv4 & IPv6 and domain name system hierarchy.
Description
This brief course will cover the OSI model layer by layer and go through some practical applications of these layers in the networking field. Students will begin to understand what is the function of each of the layers and they will be able to connect the layer number to the layer name. For instance they will know that layer 3 is the same as network layer and what protocols are functional at each of the layers and what are the responsibilities of each layer.
This will be a good foundational course for the students who want to further pursue the networking career. This can further build on this basic knowledge to take it further.
Section 1:
We start off where we left, in the previous course on “The Absolute Beginners Guide to Cybersecurity & Hacking” we dealt with the fundamental concepts such as Basic Network, CIA Triad, Network concepts, Security Operations Center and Job Roles. Section 1 starts with a refresher on network concepts, topologies etc and connects you to the previous course.
Section 2&3:
These two sections give a good insight on the OSI Model and all the Layers:
a)Physical layer b)Data link layer c)Network layer d)Transport layer e)Layered packet format f)Flow control g)Error control
f)Connection-orientedness vs connectionless g)Session layer and responsibilities h)Presentation layer and its
responsibilities i)Summary of layers
Section 4:
In this section students will learn important concepts like TCP/IP protocol suite and Domain name system hierarchy.”
Source: udemy.com
Link đăng ký miễn phí:
Ethical Hacking Foundation – Part 2
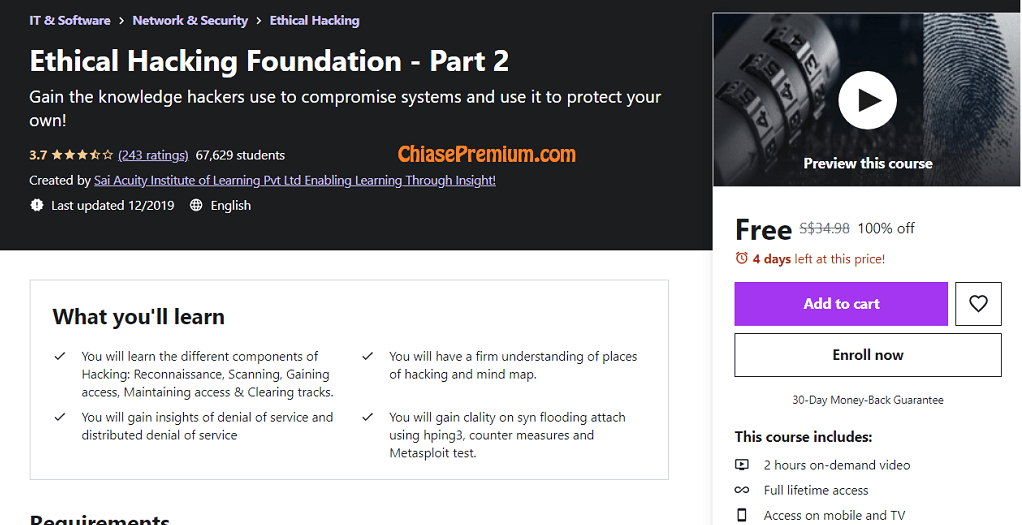
Gain the knowledge hackers use to compromise systems and use it to protect your own!
What you’ll learn
- You will learn the different components of Hacking: Reconnaissance, Scanning, Gaining access, Maintaining access & Clearing tracks.
- You will have a firm understanding of places of hacking and mind map.
- You will gain insights of denial of service and distributed denial of service
- You will gain clality on syn flooding attach using hping3, counter measures and Metasploit test.
Requirements
- You should have completed the previous course in order to continue learning. Course : Ethical Hacking Foundation – Part 1
Description
You will learn the different components of Hacking: Reconnaissance, Scanning, Gaining access, Maintaining access & Clearing tracks. You will have a firm understanding of places of hacking and mind map apart from gaining insights of denial of service, distributed denial of service, syn flooding attach using hping3, counter measures and Metasploit test.
Section 1: Components of Hacking:
Reconnaissance
Scanning
Gaining access
Maintaining access
Clearing tracks
Section 2: Ethical hacking Mindmap
Ethical hacking
Places of ethical hacking
Mind map
Section 3: DoS and DDoS
Denial of services
Symptoms of dos attack
Slow performance
Increase in spam emails
Unavailability of a resource
Loss of access to a website
Denial of access to any internet services
Distributed denial of services (DDoS)
DoS/DDoS attack techniques
Land and flood attacks
Service request floods
Section 4: SYN flooding attach using hping3
Section 5: Counter Measures
Counter-measures
DoS/DDoS countermeasure strategies
Detech and neutralize handlers
Monitoring the activities running on a system of network
Deflect attacks by load balancing
Mitigate attacks disabling unnecessary services
Intrusion detection systems
Wavelet analysis
Section 6: Metasploit test
Metasploit is so popular is the wide range of tasks that it can perform to ease the work of penetration testing to make
systems more secure. Metasploit is available for all popular operating systems.
Vulnerability
Exploit
Payload
Meterpreter
Type of Cybercrime
- The following list presents the common types of cybercrimes:
- Computer Fraud: Intentional deception for personal gain via the use of computer systems.
- Privacy violation: Exposing personal information such as email addresses, phone number, account details, etc. on social media, hacking a websites, etc.
- Identity Theft: Stealing personal information from somebody and impersonating that person.
- Sharing copyrighted files/information: This involves distributing copyright protected files such as eBooks and computer programs etc.
- Electronic funds transfer: This involves gaining an un-authorized access to bank computer networks and making illegal fund transfers.
- Electronic money laundering: This involves the use of the computer to launder money.
- ATM Fraud: This involves intercepting ATM card details such as account number and PIN numbers. These details are then used to withdraw funds from the intercepted accounts.
- Denial of Service Attacks: This involves the use of computers in multiple locations to attack servers with a view of shutting them down.
- Spam: Sending unauthorized emails. These emails usually contain advertisements.
Who this course is for:
- Students and Professionals interested in a career in Cyber Security and Ethical Hacking
- This course is for Beginners and not for advanced audience. Hence the faculty explains each concept in detail and demonstrates with relevant tools where required.
Link đăng ký miễn phí trong 24h (1000 slots):
https://www.udemy.com/course/the-absolute-beginners-guide-to-hacking-series-part-2/?couponCode=ETHICALHACKINGFREE
Source: udemy.com